Business
How to Protect Your Clients and Organization from Cybersecurity Threats

Image by TierneyMJ on Shutterstock
As the world continues to become more data-driven, the risk of cyberattacks drastically increases. For example, CPA firms are one of the main targets of breaches, seeing an 80% increase from 2014 to 2020. And ransomware or extortion cases have increased 40% since 2018. Unfortunately, less than 1% of cyberattacks are ever prosecuted.
To protect your clients and organization from cybersecurity threats, it’s crucial to understand the most common types of cyber attack.
Know the Different Types of Cyberattacks
Typically, cybercriminals target sensitive financial and personal data. The following are cyberattacks that may target your organization.
1. Phishing Attacks
Phishing schemes occur when malware-laced emails containing seemingly non-suspicious file attachments are sent to an individual’s account. These have become harder to detect over the years, and if an employee clicks on the attachment, ransomware is delivered to the system.
Generally, humans are the weakest link in an organization’s cybersecurity protocols. Cybercriminals target individual employees and management because their trust often can be exploited. While the previous example is a fairly simple but effective attack strategy, there are more advanced techniques like “spear phishing” or “whaling.”
Spear phishing is where a specific individual is targeted for their personal information. In other words, it’s a socially engineered attack to gain the trust of that individual.
Whaling attacks target high-level executives, such as the CEO or CFO. These individuals have access to the most sought-after and sensitive information, meaning they must be extremely cautious at every step. Executives receive emails regarding critical business processes from cybercriminals posing as individuals from legitimate authorities. For example, the attacker might request payment from the CEO while claiming to be a client.
The unique aspect of whaling attacks is that they often rely on information about the targeted individual available on social media, company websites, or the media. This can include the person’s title, phone number, and position. Unlike spear-phishing attacks, which target multiple individuals at the lower level, whaling specifically goes after those high-ranking executives.
2. Malware and Ransomware
Ransomware attacks work by encrypting files and blocking access to take sensitive data and systems hostage. These types of attacks often are introduced through phishing schemes, and once the data is encrypted and blocked, the target has already lost. Prevention is crucial for combating ransomware attacks.
Cybercriminals demand payment, often through cryptocurrencies like Bitcoin, in order to restore access to the systems. This type of attack has been increasing globally since 2018, with 71% of organizations affected in 2022.
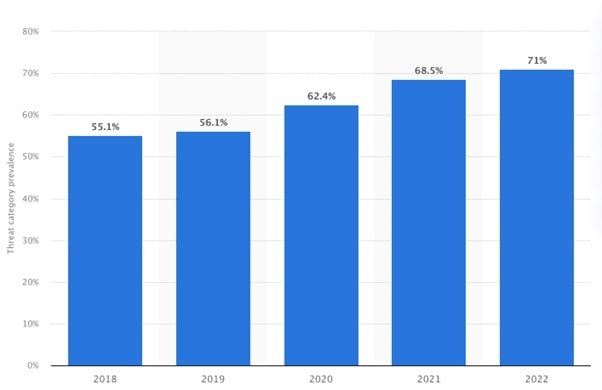
Image Source: statista.com
Ransomware attacks grow more complex and effective every year, and today they easily evade detection. These attacks, often referred to as new-age ransomware, rely on advanced distribution efforts like pre-built infrastructures. They also utilize advanced deployment techniques and crypters, which make them nearly impossible to reverse-engineer.
3. Insider Attacks
Insider threats come from an individual within the organization rather than an outside party. In many ways, the former is far more dangerous than the latter since someone within an organization already has access to sensitive data.
These attacks are more common in small organizations, largely due to the fact that individuals are granted access to multiple accounts with important data. Insider threats might not always be an attack driven by a profit motive, but rather simple carelessness that puts your organization and clients at risk.
4. Man-in-the-Middle Attacks
Man-in-the-middle (MitM) attacks occur when a cybercriminal intercepts important data communicated between two parties. The attackers first inject themselves into the conversation by breaching the communication process. The attacker can be either a passive listener or active participant, which determines whether the information is stolen or altered by an impersonator.
There are multiple methods used by attackers to gain access to the communication process, such as ARP cache poisoning and DNS cache poisoning. While these types of attacks are not as common as phishing or malware, they often have a specific intent or target. They are also often used to gain access to systems within a larger enterprise.
Results of Attacks
Cyberattacks result in severe losses in every industry, and they are capable of crippling many businesses, especially small- to medium-sized organizations.
In the case of a cyberattack, the target is forced to first pay costs to outside counsel, which protects them from litigation exposure. Outside counsel is just the beginning, as the organization then needs to pay for forensic discovery, reporting requirements, remediation, and more. All of this can add up to hundreds of thousands of dollars, which is hard for any business, especially smaller organizations.
If the breach is large enough, state and federal reporting and credit monitoring requirements can reach anywhere from $100,000 to $300,000. If the attack involves ransomware, it can result in a wide range of extra costs to pay the ransom, anywhere from thousands to millions.
Perhaps the biggest cost of all, and one that cannot be priced, is the loss of clients. With a major breach, an organization will struggle to keep the trust of both its existing clients and any prospects. The concern over client trust is especially apparent today, when there is so much sensitive data available to hackers.
How to Avoid Cyberattacks
Despite the misconception that cyberattacks mostly occur at large companies, the risk is actually much higher for small- to medium-sized organizations. The driving factor behind this is a lack of defense infrastructure and the resources needed to implement an effective cybersecurity strategy. There are ways for all organizations to avoid cyberattacks.
National Institute of Standards and Technology (NIST)
In 2017, the National Institute of Standards and Technology (NIST) at the U.S. Department of Commerce released a five-step cybersecurity framework to address the rising challenges associated with these attacks.
NIST framework:
- Identify: The first step to develop an effective cybersecurity strategy is to understand the organization’s resources and risks. This includes identifying and controlling access to data, conducting background checks, providing each employee with an individual user account, and developing clear guidelines and policies regarding cybersecurity.
- Protect: The next step is to protect your organization before it faces an attack by limiting employees’ access to data and information when necessary, patching operating systems regularly, installing software and hardware firewalls, securing networks, setting up web and email filters, encrypting sensitive business data, replacing old hardware, and implementing effective cybersecurity training programs for your employees.
- Detect: If an attack occurs, your organization should already have mechanisms in place to quickly detect it. This can be achieved by installing anti-virus, anti-spyware, and anti-malware programs. There are numerous cybersecurity tools that can help you detect vulnerabilities and threats.
- Respond: In order to reduce and contain any damage done to your company and clients, it is crucial to respond quickly. This requires preparation before the attack, such as plan development for data breaches.
- Recover: After an attack has occurred and all four other steps are followed, your organization will need to recover. To resume normal operations, back up important business data and schedule subsequent backups, look into cyber insurance, and improve any processes or technologies applicable.
How to Reduce Cyber Threats
While the NIST framework helps you develop an effective cybersecurity strategy, there are many state-of-the-art technologies and tools on the market that further increase defense.
AICPA Cybersecurity Resources
The American Institute of Certified Public Accounts (AICPA) offers many resources. Besides basic resources providing insight into the fundamentals of cybersecurity, such as guides and podcasts, the AICPA also offers various tools and resources for assessing internal risks like the CGMA Cybersecurity Risk Management Tool.
Cloud Migration
One of the best lines of defense is to adopt a cloud solution, which enhances and enables important security practices. By moving to the cloud, or developing a custom cloud hosting solution, you can also partner with experts. With the combination of a cloud system and an IT-managed services partner, your organization can protect its data from hackers.
This will enable the smooth implementation of security measures like firewalls, anti-virus, anti-spam, endpoint protection, and two-step authentication.
Cloud migration also allows for constant, 24-hour monitoring of hardware and software systems. A team of engineers can combat cyber threats as they occur and protect crucial business processes.
The best cloud services offer experienced IT professionals, assistance, disaster planning, security training for employees, and data breach drills.
VPN 2FA
Incorporating a VPN 2FA (two-factor authentication) into your business security can be incredibly beneficial. This added layer of authentication provides an extra measure of security, as all data will be encrypted and accessible only through one centralized access point with two layers of identity verification. Utilizing a VPN 2FA safeguards your valuable information from cybercriminals who may otherwise successfully penetrate traditional peripherals. Not only is VPN 2FA extremely secure, but it is also easy to use and ensures minimal disruption to regular workflows. Investing in Fortigate 2FA to your Fortigate VPN will add an essential level of protection for your business looking to guard your sensitive data.
Artificial Intelligence Tools
One of the newest tools for cybersecurity is artificial intelligence (AI). AI is becoming increasingly more complex each year, and it is useful for combating all types of cyberattacks, including lone hackers, ransomware, and malware.
AI is far superior to any one IT expert, or even an entire team of IT experts, largely due to its ability to handle nonstop cybersecurity threat developments.
AI tools can be applied in many ways, including:
Breach Detection
The key to preventing cyberattacks or stopping them before they do much damage is early detection, which is a mundane task that humans often struggle with. AI never tires, and it can operate around the clock. It constantly scans systems to improve breach detection and reduce vulnerabilities, and it frees up IT teams to put most of their focus on response.
Antivirus Software
AI can act as a superior form of antivirus software. Even the best antivirus software on the market often struggles to keep up with threats that are always evolving. AI does not require signature updates, meaning there is no lag in its threat detection, and it can close the gap by observing anomalies in real time. All of this makes it far more difficult for a hacker or malware to breach your systems.
Scanning Emails
Email activity is often the bedrock of data breaches. Most organizations have a considerable amount of email activity, but medium- to large-sized organizations are especially at risk. With 85% of employees sending more emails due to remote work, it’s especially important that email activity is constantly monitored. And many organizations are facing new cybersecurity questions as processes race to keep up with the changing world of work. For example, is Outlook HIPAA compliant? Is Gmail HIPAA compliant?
Constantly monitoring email often becomes too difficult for human eyes. Automated email scanning by AI technologies overcomes all of these challenges, and it enables employees to worry about one less aspect of cybersecurity.
Backup Processes
One of the most effective steps you can take to protect clients’ data is to implement a strong backup process. To accomplish this, daily backups must be conducted through various techniques, such as cloud backups and hard drive backups. By relying on different methods, your organization can create redundancies.
There are a few crucial factors for effective backups. First, they should take place outside of your network, or even outside of the physical space of the organization, in order to protect against natural disasters or break-ins. One way to accomplish this is to store data and backups in highly secure off-site locations that are geographically dispersed.
By relying on multiple cloud data centers in different locations, data protection is ensured through remote backups and failover protection.
Training Program for Staff
Perhaps the most crucial step you can take to protect your organization from cyber threats is to implement an efficient cybersecurity training program for your staff. All of the technology in the world is only useful if the staff is competent in cybersecurity challenges.
The majority of successful cyberattacks are a result of human error, so by having a staff that knows what to look for, your organization will have a strong defense mechanism.
One of the key aspects of such an effective training strategy is to make sure it is consistently updated. Security challenges change every day, becoming more complex and harder to address.
The first step of developing a strategy is to work on the staff’s awareness by asking it questions such as:
- Do you protect hardware by locking it when away?
- Are the passwords you use to protect sensitive information strong and complex?
- Are you aware of the various operating systems, software, and other technologies that your organization relies on?
- Do any of your personal devices carry sensitive information related to clients? And if so, do you have security protections like multi-factor authentication, encryption, or some combination of multiple on the devices?
Small- to Medium-Sized Organizations
Large enterprises often possess the resources necessary to acquire advanced technologies and software to combat cyberattacks, but the same is not true for small- to medium-sized organizations. Because of this, employee training is even more important.
If you want your staff to possess strong cybersecurity skills, you can enable them to acquire some of the top cybersecurity certifications on the market, such as the CISSP certification. Many of these are free while others have accessible costs for smaller-sized organizations.
By ensuring your staff possesses one or multiple certifications, you are essentially creating cybersecurity experts at every level of the organization. Some of the certifications are aimed at complete beginners in the cybersecurity realm, while others are meant for those with various levels of experience and knowledge.
Cybersecurity in a Data-Driven World
It is vital for your organization to develop an effective cybersecurity strategy that accounts for constant changes, as cyberattacks will only increase in complexity and threat level as time goes on.
Cyberattacks range in severity, but many result in the total devastation of small- to medium-sized organizations. Not only could they cost massive amounts of money, but they can also cause a significant loss of trust among your clients. Whether it’s phishing, malware, or ransomware attacks, your organization must take the necessary steps to protect its processes through software, hardware, and other state-of-the-art technologies.
Your staff is the first line of defense against such attacks, meaning a substantial amount of resources should be poured into it. By implementing an effective cybersecurity training program specifically developed to account for your organization’s needs, which includes enabling individual employees to obtain certifications, many potential breaches can be stopped before ever taking hold on your organization.
With the increasing frequency and sophistication of cyber attacks, businesses need to be proactive in their cyber attack prevention strategies. Implementing comprehensive cybersecurity measures such as those offered by Kelvin Zero can significantly enhance data protection, prevent potential breaches, and ensure the confidentiality and integrity of valuable information.
-
 Motivation5 years ago
Motivation5 years ago4 Fun New Hobbies To Try This Year
-

 Quotes3 years ago
Quotes3 years ago53 Motivational Gym Quotes to Fuel Your Workout
-

 Travel1 year ago
Travel1 year agoWhy You Should Travel More: The Many Benefits of Seeing the World
-

 Quotes11 years ago
Quotes11 years ago50 Most Powerful Quotes Ever Spoken
-

 Quotes4 months ago
Quotes4 months ago100 Motivational Quotes to Inspire You in 2026
-

 Quotes2 years ago
Quotes2 years ago43 Inspirational Quotes About Thoughts
-

 Quotes4 years ago
Quotes4 years ago105 Motivational Quotes by Famous People
-

 Quotes10 months ago
Quotes10 months ago100 Motivational Quotes to Start Your Day with Positivity